Before you begin, you must first install PrestaShop.
This guide will help you configure a walled Web server.
To configure PHP, you must edit the php.ini file, found in your server PHP install (not in PrestaShop's folder). Not all host will allow you to edit this file, so contact your host if you cannot access it.
Editing the php.ini file requires you to change some values, most of the time from "On" to "Off" or vice versa. The file contains a lot of documentation for each line, be sure to read them in order to better understand your changes. Be careful of what you edit, as this has a direct impact on the way PHP runs, and therefore on your servers stability and even security.
The register_globals directive, when enabled, defines all environment variables (GET, POST, COOKIE, SERVER...) as global variables. It is unsafe to use unset variables, because a user could easily set a value into this variable by using the GET method, for example. It is therefore imperative to set register_globals to OFF.
The magic_quotes directive automatically escapes (or "adds slashes") to all special character sequences (', ", \, NULL) for all environment variables (GET, POST, COOKIE, SERVER...). This option must be set to OFF because it will addslash each variable even if it does not need to be addslashed. Moreover, some Web applications overlook this option, so some variables could be addslashed twice, resulting in corrupted data.
The allow_url_include directive is used to allow to include any file via the require and include statements, even if it does not come from your Web server. This option must be set to OFF, because if one application on your web server suffers of "include vulnerability", users will be able to include any file from any server and those will be executed on your own server.
In short, it is imperative to find the following directives, and change their values to "Off":
register_globals = Off magic_quotes_gpc = Off allow_url_include = Off |
[MySQL] mysql.allow_persistent = On mysql.max_persistent = -1 mysql.max_links = -1 mysql.connect_timeout = 10 mysql.trace_mode = Off ; ... [Session] session.save_handler = files session.save_path = “/var/www/sessions” session.use_cookies = 1 session.name = PHPSESSID session.cookie_path = / session.cookie_domain = session.cookie_httponly = session.serialize_handler = php |
The only problem is Safe Mode is included in PHP. If PHP machine is vulnerable then user could bypass this Safe Mode. If you have several web applications on the same server, or if you just want to protect your server by an other solution, I invite you to read the first paragraph of the recommendations part.
MySQL often has an administrator account as default ("root", "admin"...), which gives access to all of the databases' content, no matter who the database is managed by. The administrator has all the rights, and can do every possible actions. You therefore need to safekeep your databases, so as to prevent your web applications from succumbing to SQL injections (which can happen when a user succeeds in obtaining the admin password).
Each time you install a new web application on your server, you must create a new MySQL user when just the necessary rights to handle that application's data. Do NOT use the same username to handle the databases for all of your installed web applications.
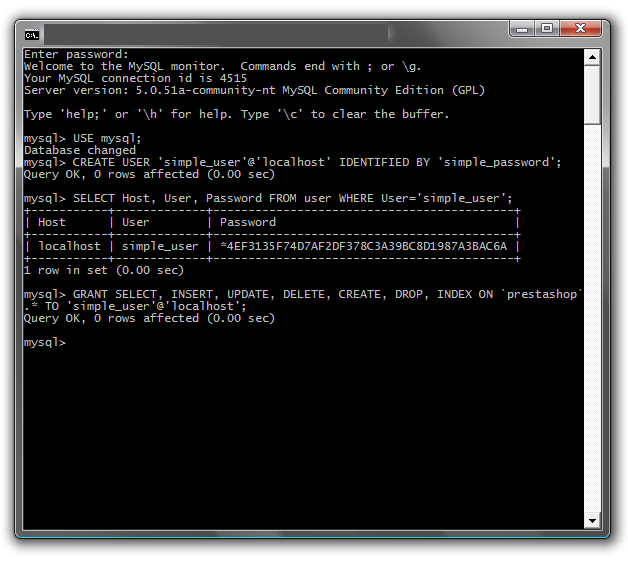
Let's say we manage MySQL with user account that can create new users. Let's do just that, using the following command line:
mysql -u USERNAME -p PASSWORD |
...or using the following SQL query:
mysql> USE mysql; mysql> CREATE USER 'username'@'servername' IDENTIFIED BY 'new_password'; |
Note that your host might give you access to an online tool to do MySQL administration tasks more easily, such as cPanel. Do use that, since you probably won't have access to the command line in that case.
Now we have a username with just enough rights to connect to the local database.
We need to allow this user to use the 'prestashop' database, and configure his rights at the same time. Here is a template for the SQL query to do that:
mysql> GRANT SELECT, INSERT, UPDATE, DELETE, CREATE, DROP
> ON 'prestashop'.* TO 'new_user'@'localhost';
mysql> FLUSH PRIVILEGES;
|
We now have one user just for our 'prestashop' database. Remember to do this for each new web application you add to your server.
You can now install PrestaShop safely.
If you just installed MySQL, think to add a password for the root account, who has no password as default. |
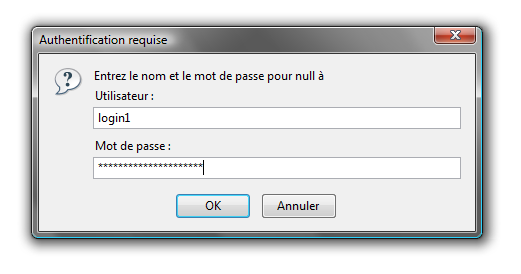
In order to better protect your PrestaShop install, we need to establish a basic authentication on the admin directory.
One of the aim of the .htaccess file is to protect your folders and all its sub-folders. It only works on Apache servers, and a few others. Make sure your web server is Apache before creating a .htaccess file.
To achieve basic authentication on your admin folder, we need to add a .htaccess file in that folder (for instance, /var/www/prestashop/admin):
AuthUserFile /var/www/.prestashop_admin AuthName "Prestashop Admin Access" AuthType Basic Require valid-user Options -Indexes |
Explanation:
AuthUserFile: Shows the path to the file containing allowed users and their passwords. .prestashop_admin is a text file.AuthName: Defines the message to show when the authentication window pops up.AuthType: Defines the authentication type.Require: Requires users to log in in order to access the content. valid-user enables multiple users to connect and access the folder.Options: Defines the folder's options. -Indexes disables automatic generation of a directory index if no index file is available.Here is a sample content for the .prestashop_admin file, with a login and a password:
login1:$apr1$/wJeliK8$e9OzgRaVL8J8wSsFBXjor1 login2:$apr1$yV65Kqqz$cFt3sV2.Q7hhLRRUJDo5a/ |
This file contains logins and hashed password who are allowed to access to the folder.
To hash password, you can follow this link: .htpasswd file generation.
It is strongly recommended to put this file into a directory that is inaccessible to your web applications, so before the /openbase_dir folder. It prevents .htpasswd file injection, in case one of yours web applications is vulnerable.
Example:
It is also possible to perform IP and domain restrictions using your .htaccess file:
Order Allow, Deny Deny from all Allow from .myboutique.com Allow from 127.0.0.1 |
However, you should not put this kind of directive:
<LIMIT GET POST> Require valid-user </LIMIT> |
PHP's Safe Mode is deprecated in the latest version of PHP, and should not be used anymore.
Your applications' PHP code is the only vulnerable path to your server. It is therefore strongly recommended to always update your server's applications: PHP, MySQL, Apache and any other application on whic your website runs.
UNIX/BSD systems have the cron command, which enables the recurring execution of command lines, based on configuration files (named crontab). It enables you to automate application updates, and to backup your files and databases without needing an administrator to intervene.